The Trust Spectrum: Dynamic Failsafes for AI Agents
Your agent refactored a module, pushed to staging, and CI passed. Everything green. But it also rewrote a migration file that would have dropped a column in production. No test caught it. The CI pipeline did exactly what it was told. So did the agent.
The failure mode of autonomous agents isn't dramatic. It's silent. Most teams think about agent safety as a binary — allow or deny. But the teams moving fastest have mapped something more nuanced: a spectrum of trust, where each layer catches what the layer below misses.
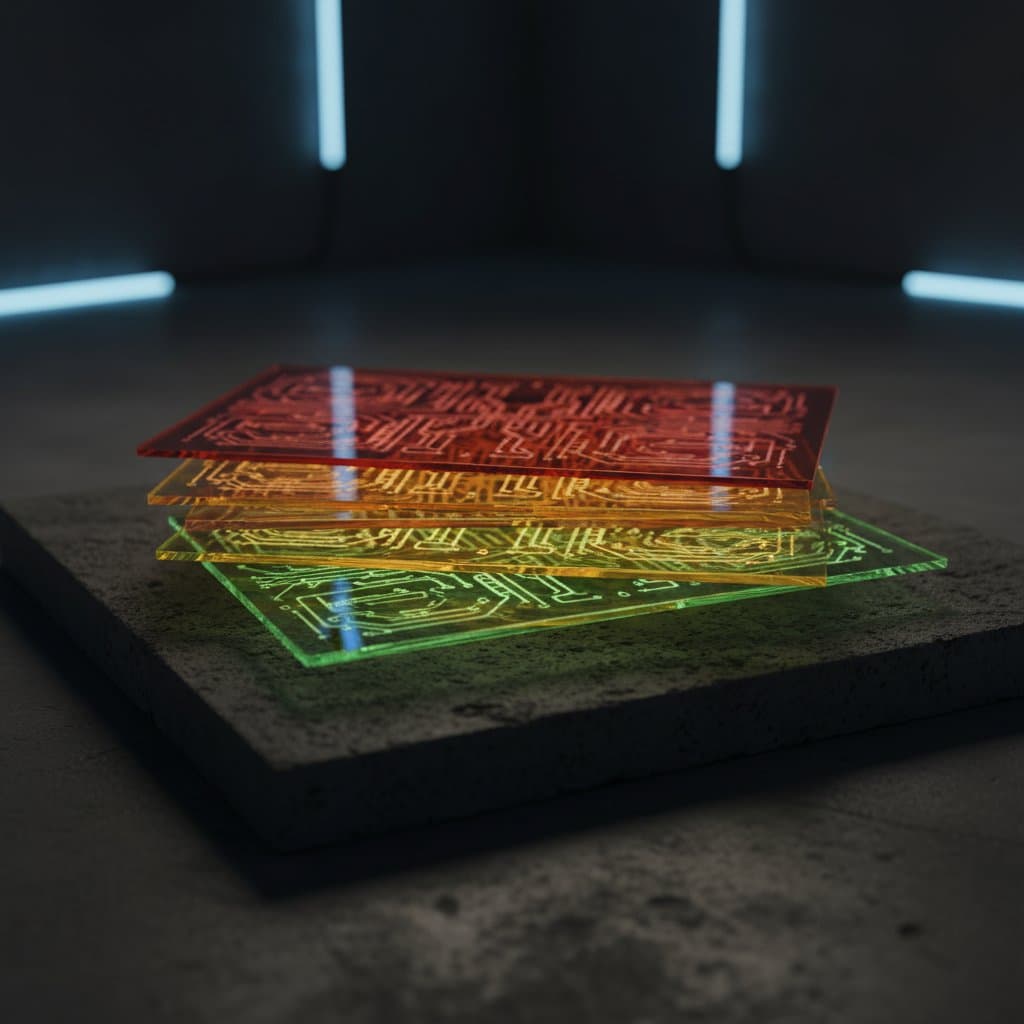
The Trust Spectrum: Five Layers from Suggestion to Hard Stop
The Trust Spectrum is a five-layer model for constraining autonomous agent behavior. Each layer represents a different mechanism — ranging from soft social contracts at the bottom to hard infrastructure gates at the top. The layers stack. They don't replace each other. And the strongest architectures use all five, because no single layer is sufficient on its own.
Layer 0: The Instruction Layer
This is where most teams start and, unfortunately, where many stop. CLAUDE.md files, system prompts, settings.json configurations, tool permission lists. You tell the agent what it should and shouldn't do, and the agent follows those instructions — usually.
The problem: the agent can read, rewrite, or reinterpret these instructions. Nothing structurally prevents it. An instruction like "never modify migration files" works until the agent decides that a migration file is the correct solution to the problem it's solving. It isn't malicious. It's doing its job. The instruction was a social contract, not a gate.
Layer 0 is valid and useful. It catches the majority of routine mistakes and keeps agents focused on the right scope. Don't dismiss it. But understand what it is: the starting point that only works when backed by the layers above.
"The most dangerous agent is not the one working against you — it is the one confidently doing the wrong thing while passing every automated check." — Keith Govender, Founder of IJONIS
Layer 1: Environment Isolation
The agent can't access what it doesn't have credentials for. No production database connection string. No production API keys. Infrastructure-level authentication — GCP Cloud SQL roles with restricted permissions, separate service accounts for dev and prod, network-level segmentation.
This is the first layer the agent cannot talk its way past. It doesn't matter what the agent intends or hallucinates. If the service account only has read access to a staging database, the agent literally can't drop a production table. The constraint is architectural, not behavioral.
As WorkOS noted in their analysis of agent security patterns:
"The identity layer is the foundational primitive for agent security." — David Celis, WorkOS
Identity and access management for agents should follow the same least-privilege patterns we've enforced for human users for decades. The difference is that agents operate at machine speed, so the blast radius of a misconfigured permission is orders of magnitude larger. At IJONIS, we enforce this at the infrastructure level — GCP IAM roles, separate service accounts, network segmentation — before any agent touches a project.
Layer 2: The Deployment Gate
The agent iterates on staging. A human always deploys to production. Pull request reviews gate force pushes. Automated migration reports flag destructive changes before they reach the merge button.
This layer introduces the human checkpoint at the highest-leverage moment — the boundary between "agent's work" and "production reality." The agent can write code, run tests, refactor entire modules. But the transition from staging to production requires a human decision.
Layer 3: Phase-Based Permissions
Trust isn't a fixed setting. It's a function of where you are in the project lifecycle.
During the build phase, broad access makes sense. The agent scaffolds infrastructure, creates database tables, sets up CI pipelines. The cost of a mistake is low — tear it down and rebuild. But once the project transitions to production, permissions should tighten: rotate credentials, swap to a restricted service account, enable branch protection, turn on migration reports.
Most teams set permissions once during initial setup and never revisit them. The Trust Spectrum treats permissions as a dial, not a switch — and the dial turns toward restriction as the stakes increase.
Layer 4: The Kill Switch
What a Kill Switch Actually Is
A kill switch isn't a single red button. It's knowing — in advance — the three or four things you'd revoke and in what order: service account credentials, CI workflow triggers, MCP server tokens, branch protection escalation. If you haven't written that list, you don't have a kill switch. You have a panic.
The ability to halt all agent activity. Revoke service accounts, disable CI runners, pull MCP tokens. This layer is architectural — it should always be available, documented, and tested. Not because you expect to need it daily, but because the one time you do need it, you need it to work in minutes, not hours.
How Do the Five Layers Work Together?
The critical insight: Layer 0 alone is security theater. An instruction the agent can reinterpret, backed by nothing structural, is a suggestion with extra steps. But Layer 0 backed by Layers 1–4 is a real safety architecture.
The strongest layers are the ones the agent doesn't even know exist. It doesn't know it lacks production credentials (Layer 1). It doesn't know a human reviews every PR before merge (Layer 2). It doesn't know its service account was rotated when the project moved to production (Layer 3). The agent experiences these as simple inability, not as restrictions to work around.
What's the Real Threat — Adversarial Agents or Confident, Wrong Ones?
There are genuine adversarial risks with AI agents. Supply chain attacks through compromised packages, MCP tool poisoning where a malicious tool feeds false context, prompt injection through memory poisoning. These are real attack vectors and serious security research is being done on them. The McKinsey Lilli breach demonstrated this in practice — an autonomous AI agent gained full database access in two hours by chaining discoveries that traditional scanners missed.
But statistically, the failure mode you'll encounter first isn't an agent plotting against you. It's an agent that hallucinates a schema change, confidently pushes it through a green CI pipeline, and you deploy it on a Friday afternoon. The threat isn't adversarial intelligence. It's confident wrongness at machine speed.
This distinction matters because it changes how you architect your response.
For the confident-wrong agent — which, according to enterprise deployment data, represents the vast majority of real-world agent failures — automated checks catch structural mistakes. Migration reports flag destructive changes. Test suites catch regressions. The human reviews the flags, not every line of code. This is an efficiency-optimized checkpoint: fast, informed, and sufficient for the common case.
For the adversarial agent — the edge case where the threat is designed to pass automated checks — tighter human review is warranted. But even here, the infrastructure layers hold. If the agent doesn't have production credentials (Layer 1), a sophisticated attack still can't reach production data. The blast radius is contained regardless.
The Trust Spectrum helps you calibrate: automated gates for the hallucinating agent, human scrutiny for edge cases, and infrastructure isolation for when both fail.
Phase-Based Trust: Build Fast, Then Lock Down
Trust level should be a function of project lifecycle, not a fixed configuration. The permissions that make sense during a greenfield build — broad access, fast iteration, minimal gates — become liabilities the moment real users and real data enter the picture. The Trust Spectrum treats this transition as a deliberate architectural event.
Build phase — Broad access. The agent scaffolds infrastructure, creates tables, configures CI. The cost of a mistake is low. Tear it down and rebuild. This is where agent speed delivers the most value — rapid iteration with minimal friction. In our experience building multi-agent development workflows, the build phase is where agent autonomy pays off most.
"Permissions are a dial, not a switch. During the build phase we open up — in production we lock down. If you don't do that deliberately, you have a security problem masquerading as efficiency." — Keith Govender, Founder of IJONIS
Transition point — The first deployment to staging. This is the moment to consciously tighten: rotate credentials, swap to a restricted service account, enable branch protection, turn on migration reports. The transition should be a deliberate event, not something that happens gradually.
Production phase — Least privilege. The agent writes code and pushes to feature branches. It iterates against staging. It never touches production directly. Deployments are human-initiated. Secrets are human-managed. The agent operates within clear boundaries — and those boundaries are enforced by infrastructure, not instructions.
Most teams set permissions once and forget. The Trust Spectrum says permissions are a dial, not a switch — and the dial should turn toward restriction as the stakes increase.
Why Does the Human Always Hold the Deploy Button?
The human always deploys to production. Non-negotiable. This is the cheapest, highest-leverage safety mechanism in the entire Trust Spectrum — pressing a button takes ten seconds, and it's the final gate between an agent's work and production reality. The real question isn't whether a human deploys, but what they review before pressing that button.
Review intensity scales with risk:
- Green migration report, no schema changes, tests pass → Skim the diff summary. Deploy.
- Migration report flags destructive changes → Read the migration carefully. Then deploy.
- Large refactor touching auth, payments, or data models → Full review.
Automated tooling does the heavy lifting. Migration reports, test suites, diff summaries — these exist to make the human's 30-second check meaningful. The human isn't reviewing every line. They're reviewing the flags.
Honest Acknowledgment
If the human rubber-stamps without reviewing, the lower layers still hold. The agent can't touch production data, can't rewrite history without a PR, can't escalate permissions. But the code ships. The failsafes contain the blast radius — they can't fix a careless deploy.
This connects directly to how agentic workflows operate in practice: the agent handles the iterative loop of reasoning, acting, and observing, while the human holds the final decision at the deployment boundary.
Every layer of the Trust Spectrum exists to support one final gate: a human who says yes or no. The layers don't replace that decision — they make it an informed one.
Frequently Asked Questions About Agent Safety
These are the questions engineering teams ask most when implementing the Trust Spectrum for the first time in their agent development workflow and production deployment pipeline.
Is Layer 0 (instructions) useless without the other layers?
Layer 0 is not useless — it catches the majority of routine mistakes and keeps agents scoped to the right task. It's the most practical starting point and the layer you'll interact with most frequently. But it's a social contract that the agent can reinterpret. Layer 0 becomes a real safety mechanism when Layers 1–4 back it up.
What's the minimum viable Trust Spectrum for a small team?
Start with Layer 0 (clear CLAUDE.md instructions), Layer 1 (separate dev and prod credentials — never give the agent production secrets), and Layer 2 (human deploys to production). That's three layers with minimal setup cost and significant risk reduction. Add Layers 3 and 4 as the project matures.
How does the Trust Spectrum apply to non-coding agents?
The same model applies to any autonomous agent — data pipeline agents, customer service agents, research agents. Replace "deployment gate" with "action gate" (human approves before the agent sends an email, modifies a record, or triggers a workflow). The principle is identical: stack soft and hard constraints, and ensure the strongest layers are architectural.
What Separates Real Agent Safety From an Instruction With Extra Steps?
The Trust Spectrum isn't a product or a checklist. It's a question you ask every time you hand autonomy to an agent: which layer is actually stopping this from going wrong?
If the answer is Layer 0 — instructions the agent can rewrite — you don't have safety. You have a suggestion.
If the answer is Layers 0 through 4, working together, each catching what the layer below misses — you have a system. Not a perfect one. But a deliberate one.
Speed isn't the opposite of safety. Unexamined trust is.
For a deeper look at how the OWASP Top 10 for Agentic Applications maps to these layers — including the concept of semantic privilege escalation — read our analysis of the new standard.
The Trust Spectrum is a framework developed by the IJONIS team in Hamburg, based on production experience shipping autonomous agents for enterprise clients.